It could potentially threaten your PC.
- A recent study published by ESET details a shocking revelation.
- BlackLotus, malware sold on the black market for $5,000, is reportedly able to bypass your Secure Boot mechanism.
- The rumor has been going on since October 2022.
If there’s a public enemy number-one for Windows 11 users since October 2022, that would have been BlackLotus. At that time, the UEFI bootkit malware was rumored to be the only thing that could pass any defense in the cyber landscape.
For just $5,000, hackers on black forums could have an access to this tool and bypass Secure Boot on Windows devices.
Now, it seems like what has been feared for months is true, at least according to ESET’s recent study done by analyst Martin Smolár.
The number of UEFI vulnerabilities discovered in recent years and the failures in patching them or revoking vulnerable binaries within a reasonable time window hasn’t gone unnoticed by threat actors. As a result, the first publicly known UEFI bootkit bypassing the essential platform security feature – UEFI Secure Boot – is now a reality.
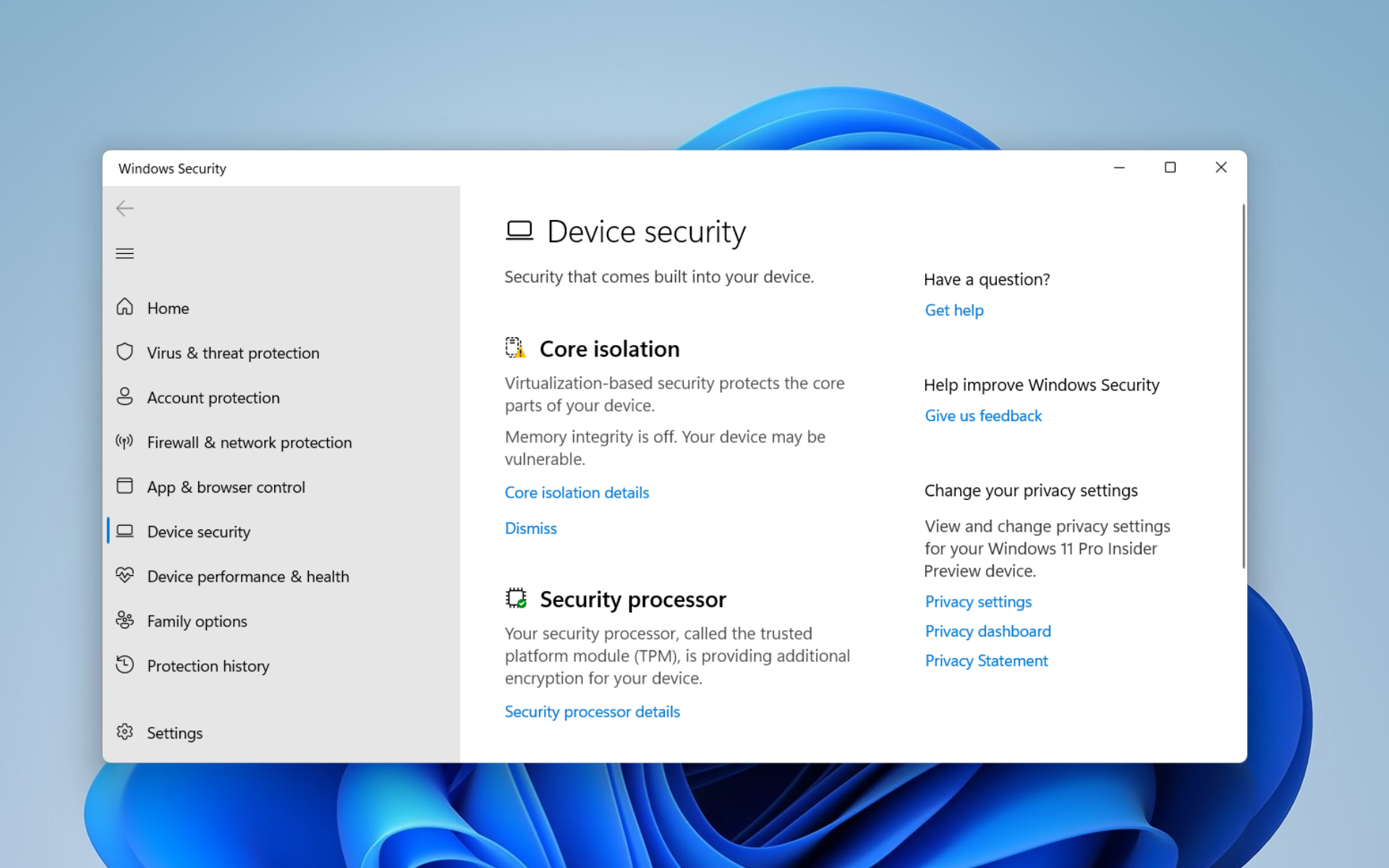
When you boot up your devices, the system and its security load first before anything else to disarm any malicious attempt at accessing the laptop. BlackLotus, however, targets UEFI so that it loads before anything else.
Matter of fact, it’s able to run on the latest Windows 11 system with the Secure Boot feature enabled.
BlackLotus exposes Windows 11 through its CVE-2022-21894 vulnerability. While it was patched in Microsoft’s January 2022 update, the malware takes advantage of this by signing binaries that have not been added to the UEFI revocation list.
Once installed, the bootkit’s main goal is to deploy a kernel driver (which, among other things, protects the bootkit from removal), and an HTTP downloader responsible for communication with the C&C and capable of loading additional user-mode or kernel-mode payloads.
Smolár also writes that some of the installers do not proceed if the host uses locales from Romanian/Russian (Moldova), Russia, Ukraine, Belarus, Armenia, and Kazakhstan.
Details of this first emerged when Kaspersky’s Sergey Lozhkin saw it being sold on black markets with the aforementioned price tag.
What do you think about this latest development? Let us know in the comments!
Start a conversation


Leave a Comment