Readers help support Windows Report. When you make a purchase using links on our site, we may earn an affiliate commission.
Read the affiliate disclosure page to find out how can you help Windows Report effortlessly and without spending any money. Read more
It’s now known that threat actors will use every technology available, including AI, to release all sorts of threats, from ransomware to phishing, malware, and more.
Microsoft platforms, such as Outlook or Microsoft 365 are some of the most affected by it: for instance, in 2022, alone, more than 80% of Microsoft 365 accounts were hacked, at some point.
However, Microsoft says its Microsoft Incident Response system can employ a variety of cybersecurity tools, from Microsoft Defender for Identity to Microsoft Defender for Endpoint to eradicate such threats in a matter of minutes. Plus, together with the new Copilot for Security, Incident Response can swiftly deal with any kind of cybersecurity issues without worrying that the system is compromised.
The Redmond-based tech giant showcased an example where an organization was targeted by the Qakbot modular malware, which spread to the servers after being accessed in an email.
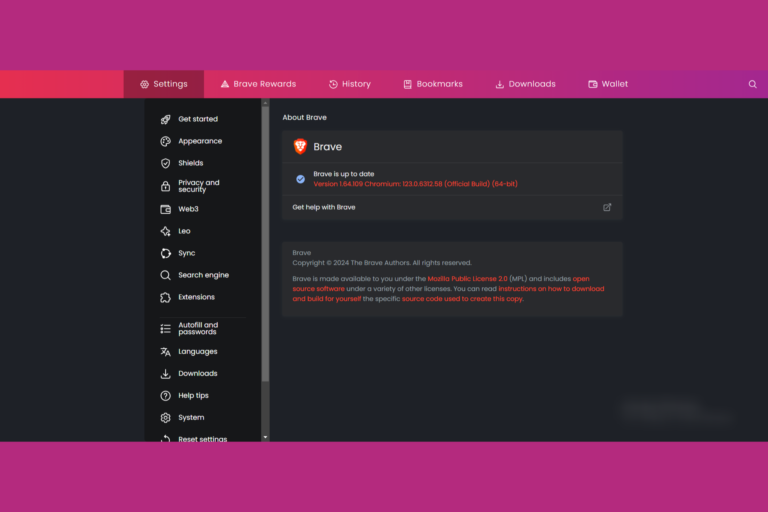
The Qakbot attacks the infrastructure through a variety of means, and it’s used to steal credentials including but not limited to financial data, locally stored emails, system passwords or password hashes, website passwords, and cookies from web browser caches.
Microsoft stepped in, and with the Incident Response system, it was able to deal with the issue in a multi-platform approach, as it states:
Microsoft Incident Response stepped in and deployed Microsoft Defender for Identity—a cloud-based security solution that helps detect and respond to identity-related threats. Bringing identity monitoring into incident response early helped an overwhelmed security operations team regain control. This first step helped to identify the scope of the incident and impacted accounts, take action to protect critical infrastructure, and work on evicting the threat actor. Then, by leveraging Microsoft Defender for Endpoint alongside Defender for Identity, Microsoft Incident Response was able to trace the threat actor’s movements and disrupt their attempts to use compromised accounts to reenter the environment. And once the tactical containment was complete and full administrative control over the environment was restored, Microsoft Incident Response worked with the customer to move forward to build better resiliency to help prevent future cyberattacks.
Microsoft
One of the most interesting aspects of the Microsoft Incident Response is its ability to use honeytokens, a security method that employs decoy accounts to trick and lure threat actors into believing they’re targeting real accounts.
The decoy accounts are called honeytokens, and they can provide security teams with a unique opportunity to detect, deflect, or study attempted identity attacks. The best honeytokens are existing accounts with histories that can help hide their true nature. Honeytokens can also be a great way to monitor in-progress attacks, helping to discover where attackers are coming from and where they may be positioned in the network.
Microsoft
The Redmond-based tech giant advises customers to get in touch with Microsoft so that the Incident Response system can be properly implemented when dealing with cyber threats or cyberattacks.
You can read the full blog post here.


Leave a Comment