Readers help support Windows Report. When you make a purchase using links on our site, we may earn an affiliate commission.
Read the affiliate disclosure page to find out how can you help Windows Report effortlessly and without spending any money. Read more
We previously pointed out how it takes less than a minute to break into BitLocker encryption using a Raspberry Pi Pico. Now, as it turns out, modern-day PCs with TPM 2.0, the latest version, running Windows 11, too, are at risk of key sniffing. And it doesn’t take much more effort!
It was pointed out by a security researcher who goes by the name stacksmashing on X (formerly Twitter). This was in response to several users claiming that modern-day laptops are highly secure and bypassing BitLocker encryption is not possible.
The security researcher had previously, in a YouTube video, detailed the process to retrieve the BitLocker recovery key and access the encrypted data.
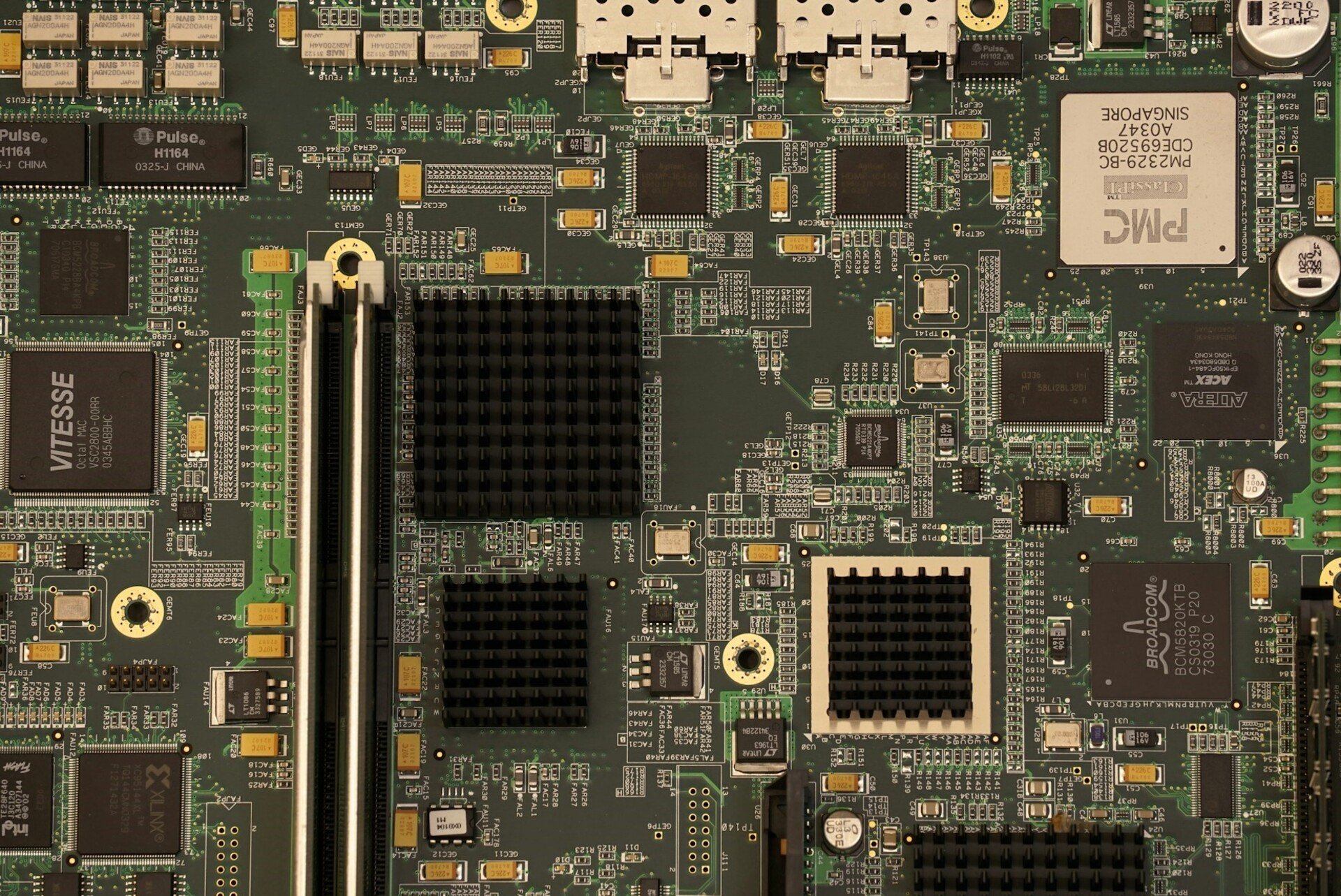
Since the process employed here utilizes the unsecured communication between the CPU and TPM (Trusted Platform Module) chip, it’s possible to retrieve the BitLocker encryption key as long as the two are distinctly placed.
BitLocker key retrieval on modern laptops
In another post, Stu Kennedy, also a security researcher, explained how soldering directly to the right pads on a Lenovo X1 Carbon Gen 11, released in April 2023, allowed the logic analyzer to get the BitLocker’s VMK (Volume Master Key).
On his GitHub page, Kennedy has listed the steps to retrieve the BitLocker key from several modern-day laptops, along with the hardware required for the job. The list of laptops includes Microsoft Surface Pro 3 and Dell Lattitude E5470 (amongst others), both with TPM 2.0 chips.
As per Kennedy, one of the ways to stay safe from this vulnerability is to enable BitLocker with a security key or PIN. This will act as pre-boot authentication and prevent sniffing devices from retrieving the VKM since it will be released only after the security key is entered.
Also, the problem appears to affect devices featuring a separate, dedicated TPM chip.
Should I be concerned about this?
If you are too concerned, don’t be!
The vulnerability can only be exploited as long as the threat actor has physical access to the device. Accessing over the web won’t do!
You should be more worried about infecting the PC with malware from the web. And for that, practicing good cyber hygiene and an effective antivirus solution are all you need.
Such vulnerabilities have existed in the past and were rectified over the course of time. In this case, too, we might see built-in TPM chips in the CPU or optional pre-boot authentication enforced by manufacturers to eliminate the risks.
What are your thoughts on it? Share with us in the comments section below.


Leave a Comment